What Services Do I Need Running On My Computer

In this article, I tried to prepare a write-up for the "Network Services" room ontryhackme.
[Task 1] Expanding Your Knowledge
This room volition explore common Network Service vulnerabilities and misconfigurations, simply in gild to practice that, nosotros'll need to do a few things showtime!
#ane Ready? Let'south go going!
ANSWER: No answer needed
[Chore 2] Understanding SMB
SMB – Server Bulletin Block Protocol – is a customer-server communication protocol used for sharing access to files, printers, serial ports and other resource on a network.
#one What does SMB represent?
SMB – Server Message Cake Protocol – is a customer-server communication protocol used for sharing access to files, printers, serial ports and other resources on a network.
Answer: Server Message Cake
#2 What type of protocol is SMB?
The SMB protocol is known as a response-request protocol.
Respond: response-request
#3 What practise clients connect to servers using?
Clients connect to servers using TCP/IP.
ANSWER: TCP/IP
#iv What systems does Samba run on?
Samba, an open source server that supports the SMB protocol, was released for Unix systems.
Respond: Unix
[Task iii] Enumerating SMB
Earlier we begin, make sure to deploy the room and give information technology some time to boot. Delight be aware, this can take upward to five minutes so be patient!
I ran the nmap query below. But this query took more than twenty minutes.
nmap -A -T4 -p- <car IP> Nosotros will answer the questions co-ordinate to the results in the pictures below.


#1 Conduct annmap scan of your choosing, How many ports are open?
Port 22, Port 139 and Port 445 are open.
ANSWER: 3
#ii What ports isSMB running on?
You tin run across the answer in the first picture above. SMB appears to be open on 2 ports.
Answer: 139/445
#3 Let's get started with Enum4Linux, conduct a full basic enumeration. For starters, what is theworkgroupname?
Let's run this command.
enum4linux -A <machine IP> The result of the command executed is equally follows:

ANSWER: WORKGROUP
#iv What comes up equally thename of the machine?

ANSWER: POLOSMB
#5 What operating systemversion is running?

ANSWER: half dozen.1
#6 What share sticks out as something we might desire to investigate?

Reply: profiles
[Task 4] Exploiting SMB
While at that place are vulnerabilities such as CVE-2017-7494 that can let remote lawmaking execution by exploiting SMB, yous're more probable to encounter a situation where the best way into a organisation is due to misconfigurations in the organization. In this case, we're going to be exploiting bearding SMB share access- a common misconfiguration that can allow us to gain information that will pb to a shell.
#i What would be the correct syntax to access an SMB share chosen "hush-hush" as user "adjust" on a car with the IP 10.10.10.2 on the default port?
ANSWER: smbclient //10.10.10.2/secret -U conform -p 445
#2 Neat! At present y'all've got a hang of the syntax, let'southward accept a go at trying to exploit this vulnerability. You have a list of users, the name of the share (smb) and a suspected vulnerability.
Reply: No answer needed
#3 Does the share allow anonymous admission? Y/Northward?
Permit'southward run this command to access "Anonymous" user. When the organization inquire the countersign, then but click "enter". Y'all don't need to enter the "countersign" value.
smbclient //10.10.10.2/profiles -U anonymous -p 445 
ANSWER: Y
#4 Peachy! Have a look around for any interesting documents that could contain valuable information. Who can we assume this profile folder belongs to?

You tin can meet the "interesting certificate". Allow'south get this document. You tin can run this command in smb.
get "Working From Home Information.txt" [output name] 
Permit's read the downloaded file on our own computer. The proper noun at the first of the text is the reply to our question.

ANSWER: John Cactus
#v What service has been configured to allow him to work from home?

The ".ssh" file is an SSH configuration file.
ANSWER: ssh
#6 Okay! Now we know this, what directory on the share should we await in?

Answer: .ssh
#7 This directory contains authentication keys that allow a user to authenticate themselves on, and then access, a server. Which of these keys is most useful to us?
Let's check what is in the ".ssh" file.

ANSWER: id_rsa
#8 Download this file to your local auto, and change the permissions to "600" using "chmod 600 [file]". Now, use the information you have already gathered to piece of work out the username of the account. And then, use the service and key to log-in to the server. What is the smb.txt flag?
Showtime, let'southward download the "id_rsa" and "id_rsa.pub" files to our own computer.
get id_rsa [outputname] get id_rsa.pub [outputname] 

Modify the permissions of the "my_id_rsa" file to 600 using:
chmod 600 [your id_rsa file] 
We can connect with ssh considering we have "id_rsa" file of "cactus" user.
ssh -i [your id_rsa file] cactus@<targer IP> 

ANSWER: THM{smb_is_fun_eh?}
[Task five] Understanding Telnet
#1What is Telnet?
Telnet is an application protocol.
Answer: awarding protocol
#2What has slowly replaced Telnet?
Telnet has been replaced by SSH in most implementations.
ANSWER: ssh
#3How would you connect to a Telnet server with the IP ten.10.10.3 on port 23?
ANSWER: telnet 10.ten.10.3 23
#fourThe lack of what, means that all Telnet communication is in plaintext?
ANSWER: encryption
[Job half dozen] Enumerating Telnet
You lot tin use this nmap browse:
nmap -T4 -p- <machine IP> 

#oneHow manyports are open on the target car?
ANSWER: ane
#2Whatport is this?
Answer: 8012
#threeThis port is unassigned, merely even so lists theprotocol it'south using, what protocol is this?
Y'all tin see the answer in the 2d motion-picture show above.
Answer: tcp
#ivNow re-run thenmap scan, without the-p- tag, how many ports show up equally open?

Answer: 0
#fiveHere, nosotros run across that by assigning telnet to anot-standard port, it is non part of the common ports list, or acme chiliad ports, that nmap scans. Information technology's important to try every bending when enumerating, as the information you lot gather here will inform your exploitation stage.
Answer: No answer needed
#6Based on the title returned to us, what do we think this port could beused for?

According to the Nmap scan, but one port appears to be open. All other ports are closed. In this instance, we tin call the "backdoor" port only for the open up port.
Yous tin as well see the text "SKIDY'S BACKDOOR" clearly in the picture to a higher place.
Reply: a backdoor
#7Who could it belong to? Gathering possibleusernames is an important step in enumeration.
You tin come across the proper noun in picture above.
Answer: Skidy
#eightEver proceed a notation of data you find during your enumeration stage, and so y'all tin can refer back to it when you move on to try exploits.
Answer: No answer needed.
[Task 7] Exploiting Telnet
#aneOkay, let's try and connect to this telnet port! If you get stuck, accept a look at the syntax for connecting outlined to a higher place.
Answer: No answer needed
#iiGreat! It's an open telnet connection! What welcome message exercise we receive?

Telnet Connectedness = telnet <IP> <port number>
ANSWER: SKIDY'S BACKDOOR.
#3Let'due south attempt executing some commands, do nosotros get a return on any input we enter into the telnet session? (Y/Northward)

ANSWER: N
#4Hmm… that's foreign. Allow's check to see if what we're typing is being executed as a system command.
Respond: No answer needed
#5Start a tcpdump listener on your local machine using:"sudo tcpdump ip proto \\icmp -i tun0" This starts a tcpdump listener, specifically listening for ICMP traffic, which pings operate on.

Reply: No reply needed
#6At present, apply the control"ping [local tun0 ip] -c 1"through the telnet session to encounter if we're able to execute system commands. Exercise we receive any pings? Note, you lot demand to preface this with .RUN (Y/N)
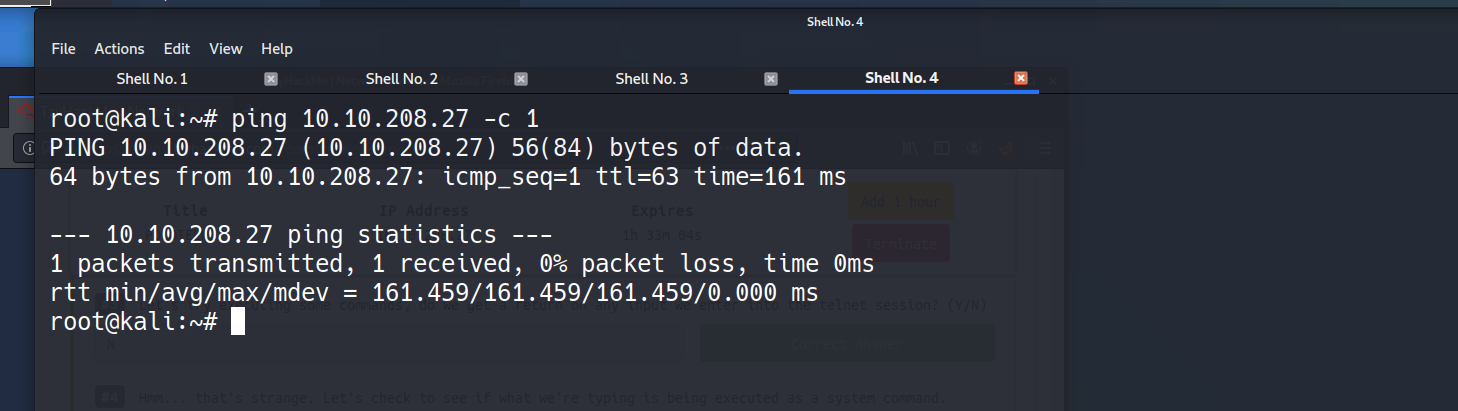

ANSWER: Y
#7Great! This means that nosotros are able to execute arrangement commands AND that we are able to reach our local motorcar. Now let's have some fun!
Answer: No respond needed
#8 What word does the generated payload start with?

Reply: mkfifo
#9Perfect. We're nearly there. Now all we demand to do is start a netcat listener on our local machine. What would the control await like for the listening port nosotros selected in our payload?
Respond: nc -lvp 4444
#xCorking! Now that's running, we need to copy and paste our msfvenom payload into the telnet session and run it equally a command. Hopefully- this will requite us a shell on the target automobile!

Reply: No answer needed
#11Success! What is the contents of flag.txt?

ANSWER: THM{y0u_g0t_th3_t3ln3t_fl4g}
[Task 8] Understanding FTP
#aneWhat communications model does FTP use?
FTP operates using a client-server protocol.
Answer: client-server
#2What'due south the standard FTP port?
Respond: 21
#3How many modes of FTP connexion are there?
The FTP server may support either Active or Passive connections, or both.
ANSWER: 2
[Chore 9] Enumerating FTP
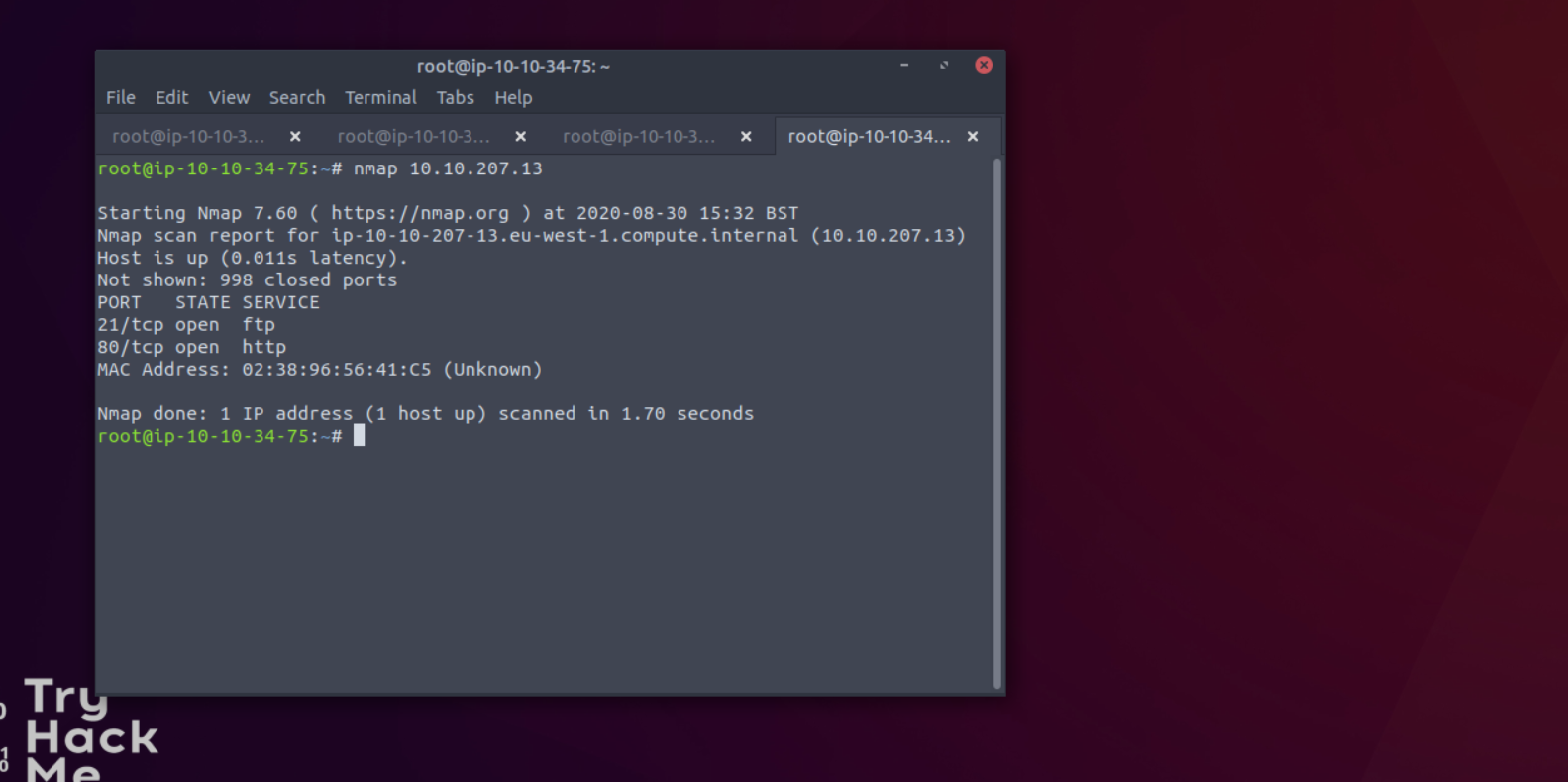
#iRun annmap scan of your choice. How manyports are open on the target car?
ANSWER: 2
#2Whatport is ftp running on?
ANSWER: 21
#3Whatvariantof FTP is running on it?

Respond: vsftpd

What is the name of the file in the anonymous FTP directory?
You will be asked for a username and password. For "anonymous" user ;
- username: anonymous
- password: bearding
Answer: PUBLIC_NOTICE.txt
#5 What practise we think a possible username could be?

Respond: mike
#half dozenGreat! Now we've got details about the FTP server and, crucially, a possible username. Permit's see what nosotros can do with that…
ANSWER: No answer needed
[Task 10] Exploiting FTP
#1What is the password for the user "mike"?
We should run this command:
hydra -t iv -l mike -P /usr/share/wordlists/rockyou.txt -vV <Machine IP> ftp 
ANSWER: countersign
#2Bingo! Now, let's connect to the FTP server as this user using"ftp [IP]"and entering the credentials when prompted
ANSWER: No answer needed
#threeWhat is ftp.txt?


Reply: You can capture the flag past yourself 🙂
[Task xi] Expanding Your Knowledge
#oneWell washed, you did information technology!
Answer: No answer needed
So far, I have tried to explain the solutions of the questions as detailed as I can. I hope it helped you. Run into you lot in my next write-upwards.
Source: https://fthcyber.com/2020/09/30/network-services-writeup-tryhackme/
Posted by: corleywittentiou.blogspot.com


0 Response to "What Services Do I Need Running On My Computer"
Post a Comment